What is Technical Debt in Software Development? A Guide

Your MVP is live. Users are signing up. A pilot customer wants one more feature before they commit. Your team says it should be a quick change, then it takes two weeks and breaks checkout, notifications, and analytics on the way out.
That’s the moment founders usually ask the wrong question. They ask, “Why is engineering suddenly slow?” The better question is, “What have we already borrowed against this codebase?”
If you’re asking what is technical debt in software development, think of it as the bill for shortcuts. You shipped faster earlier, but now every new change costs more than it should. That cost doesn’t stay inside engineering. It shows up in missed roadmap dates, fragile releases, slower sales follow-through, and weaker investor confidence during due diligence.
As a fractional CTO, I’ll give you the blunt version. Technical debt is not a normal startup inconvenience you ignore until after funding. It’s a direct input into speed, reliability, and valuation. Founders who treat code as a disposable prototype usually pay for it when they try to scale. Founders who treat code as an asset build a stronger company.
The Hidden Drag on Your Startup's Growth
A founder gets through the hardest part first. They ship. The app works well enough to prove demand. Early customers are engaged. Then growth exposes the part nobody wanted to fund properly the first time.
The team starts avoiding certain files because every change creates side effects. Releases get tense. Small features become negotiation exercises between product and engineering because nobody trusts the estimate anymore. Developers aren’t lazy, and they usually aren’t incompetent. They’re working inside a system that’s become expensive to change.
When speed turns into friction
Startups often celebrate the first phase of velocity. That makes sense. Shipping matters. The problem starts when that first sprint becomes the architecture plan.
Common founder symptoms look like this:
Features keep slipping: Work that sounded simple in planning expands once engineers uncover brittle dependencies.
Bugs appear in unrelated areas: A change to billing breaks onboarding because the system is too tightly coupled.
The team loses confidence: Engineers hesitate to deploy because the blast radius of a mistake is unclear.
Roadmap discussions get political: Product wants speed. Engineering wants cleanup. Both are reacting to the same underlying debt.
Technical debt isn’t visible on your homepage, but it’s often the real reason your roadmap starts drifting.
Why founders misread the problem
Many founders interpret this slowdown as a hiring issue. They assume they need more developers. Sometimes they do. But adding headcount to a debt-heavy codebase often multiplies confusion rather than output.
A messy system punishes every new engineer with longer onboarding, weaker context, and more accidental damage. You don’t fix that by stacking more people into it. You fix it by reducing the hidden cost of change.
Technical debt acts like an invisible mortgage on your product. At first, the payment feels manageable. Then interest takes over. Every feature carries repayment costs from old shortcuts, weak architecture, and neglected operational discipline. That’s when growth starts feeling heavier than it should.
What Exactly Is Technical Debt
Ward Cunningham coined the term technical debt in 1992 to describe a trade-off every startup makes under pressure. You ship faster today by accepting a cleanup cost tomorrow. The problem for founders is simple. If that liability stays small and controlled, it can help you learn faster. If it spreads through the product, it starts reducing development speed, raising delivery risk, and weakening your position in investor diligence.
One practical way to track it is the technical debt ratio (TDR). A 10% TDR means teams spend roughly one hour fixing issues for every ten hours of new work, according to GetDX on technical debt ratio. Founders should treat that ratio like a balance sheet signal. A rising number means future product capacity is already spoken for.
The debt metaphor founders should use
Financial debt can fund expansion when the return is clear and repayment is planned. Technical debt works the same way. The question is not whether debt exists. The question is whether you took it on deliberately, priced the risk correctly, and assigned a repayment date.
That distinction matters in fundraising.
A founder who can explain why the team made a shortcut, where it sits, what it affects, and when it will be repaid sounds disciplined. A founder who says, "the code is messy, but we can clean it up later," sounds like someone carrying hidden liabilities into a financing process.
If you hard-code a workflow to validate demand and schedule cleanup right after the experiment, that is strategic debt. If the team keeps layering patches into a fragile payment flow because no one owns architecture, that is operational sloppiness. Investors can tell the difference.
Four forms of debt you need to recognize
You do not need academic taxonomy. You need pattern recognition that maps directly to business risk.
Intentional debt
You chose speed on purpose.
Example: the team skips a cleaner implementation because a customer demo is next week and the feature may never become core product behavior. That can be a sound decision if the shortcut is documented, isolated, and tied to a clear cleanup trigger.
Accidental debt
You created risk without meaning to.
This usually comes from incomplete technical judgment, rushed implementation, or product changes that outgrow the original design. A common source is premature abstraction in software engineering, where a team builds flexibility before it has enough evidence to know what should stay flexible.
Code and design debt
This is the form founders notice first. Duplicated logic, weak module boundaries, unclear ownership of business rules, inconsistent naming, and architecture that only works through workarounds all belong here.
It shows up fast in due diligence. If a basic feature requires changes across too many files, or engineers cannot say with confidence where pricing, permissions, or billing logic lives, your system is already taxing future growth.
Infrastructure and process debt
This category hurts valuation more than many founders expect. Manual deployments, low test coverage, stale dependencies, weak observability, poor incident response, and release steps that depend on one senior engineer all increase operating risk.
Practical rule: If your product only ships safely when one specific person is online, your company is carrying debt that will show up in diligence.
Not all debt deserves the same response
Debt in an experiment is one thing. Debt in authentication, billing, data integrity, or deployment is a direct threat to revenue and investor confidence.
Treat debt by business exposure, not by how annoying it feels to the engineering team. Core-path debt gets repaid first because it affects customer trust, security posture, uptime, and the credibility of your roadmap. Peripheral debt can wait for a defined period if it supports learning. Founders who make that distinction clearly tend to preserve both shipping speed and company value.
How Startups Accumulate Technical Debt
Technical debt rarely appears because a team wants low quality. It appears because the business keeps forcing trade-offs under pressure. Most of those decisions feel rational in the moment.
A founder needs a product for a demo. A pilot customer wants custom behavior. The roadmap shifts after user feedback. A junior engineer reaches for the fastest fix because no senior architect is shaping the system. None of that is unusual. What matters is whether those decisions are controlled or cumulative.
The startup pressures that create debt
The first source is MVP urgency. Founders want proof, not perfection. That’s correct. But many teams confuse “lean” with “sloppy.”
Typical examples include:
Hard-coded decisions: API keys, pricing logic, access rules, or workflow states live in code because configuration would take longer.
Skipped tests: The team promises to add automated coverage later and almost never comes back.
Temporary integrations that become permanent: A fast connector gets shipped for one customer and ends up serving the whole product.
Unclear ownership: No one is responsible for long-term architecture, so local fixes pile up.
Product changes often make debt worse
Debt compounds when product direction changes faster than the codebase can absorb. Startups pivot. That’s normal. What hurts is pivoting on top of brittle foundations without refactoring the old assumptions out of the system.
One common mistake is abstracting too early in the wrong places while staying too rigid in the places that matter. If your team needs a useful reference on that trap, this write-up on premature abstraction in software engineering is worth reading. Founders often push teams to “make it scalable” before the product has earned complexity, then underinvest in the architecture that needs durability.
Skill gaps create hidden liabilities
Early teams are often uneven. You might have one strong product-minded engineer and two developers who can ship features but don’t yet see architectural consequences. That doesn’t make them bad hires. It does mean debt can accumulate unnoticed.
A team without experienced technical leadership tends to create debt in three ways:
Pattern | What it looks like | Why it hurts later |
|---|---|---|
Local optimization | Fast fixes inside one module | The system becomes inconsistent |
Weak boundaries | Business logic spread across frontend, backend, and scripts | Simple changes require broad edits |
Operational shortcuts | Manual deploys and sparse monitoring | Small failures become bigger incidents |
Founders shouldn’t moralize this. Startups create debt because speed matters. The mistake lies in pretending those trade-offs disappear once the feature ships. They don’t. They sit on the balance sheet of your product until engineering has to pay them back.
The True Cost to Your Business and Valuation
A founder closes a strong quarter, opens a data room, and expects investors to focus on growth. Then technical diligence starts. Release frequency is inconsistent. Core workflows depend on one engineer. Security fixes sit in backlog. The discussion shifts fast from upside to risk.
Technical debt does that. It converts engineering shortcuts into valuation pressure.
The Consortium for IT Software Quality estimates the annual cost of poor software quality, largely driven by technical debt, at $2.41 trillion in the United States, with Southwest Airlines offering a concrete example. Technical debt in scheduling systems was a major contributor to 13,000 canceled flights during the 2022 holiday season, as summarized by DevDynamics on the cost of technical debt.
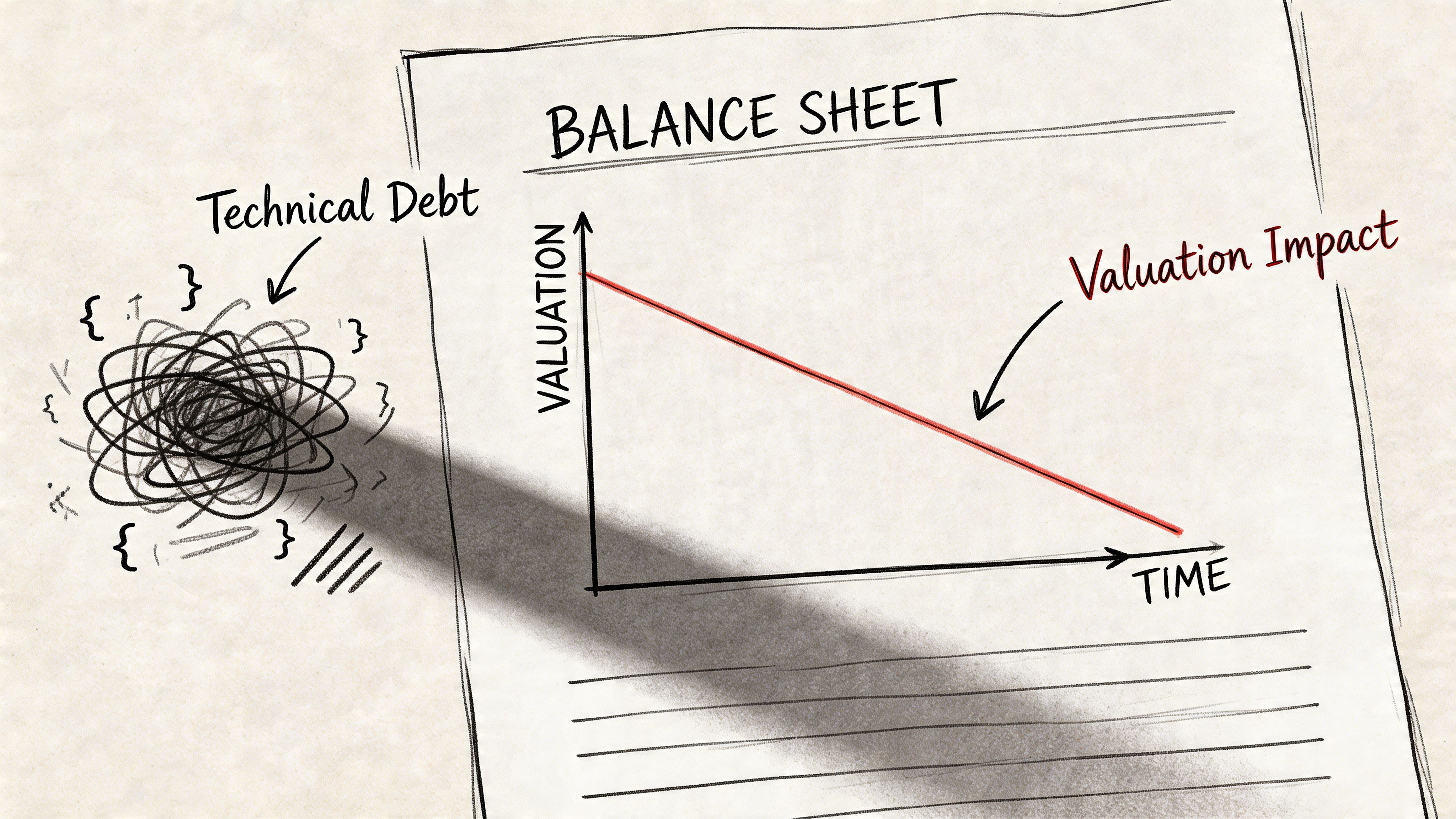
A startup does not need airline scale to suffer the same pattern. Debt works like a financial obligation. It buys speed today, then charges interest through slower execution, higher operating risk, and lower confidence in future performance. Investors care because that interest gets paid with their capital.
Debt reduces enterprise value before it causes a visible failure
The first hit rarely looks dramatic. It shows up in missed release dates, rising support load, and product decisions shaped by what the code can tolerate instead of what the market needs. That is not an engineering inconvenience. It is a growth constraint.
Here is where founders feel the cost:
Revenue slows: Sales hears “not yet” on integrations, security requirements, and product gaps that should have shipped already.
Margins shrink: Engineers spend more time maintaining brittle systems and less time building differentiated features.
Forecasting gets weaker: Roadmaps lose credibility because every estimate hides unknown cleanup work.
Customer risk rises: Bugs, slow performance, and reliability issues increase churn pressure, especially in B2B accounts.
Hiring cost increases: Strong engineers hesitate when the codebase looks expensive to inherit.
This interest payment compounds in the only place that matters. Company value. If each new feature takes longer to ship and creates more operational risk, your startup becomes less scalable, less predictable, and less attractive as an investment.
Investors price technical debt as future dilution
Investors do not expect a pristine codebase. They do expect evidence that your architecture can support growth without a rewrite right after the round. If they see a product that needs cleanup before it can scale, they treat that cleanup as a use of proceeds.
That changes the conversation in three ways.
First, technical debt weakens your efficiency story. A company that needs twelve months of platform repair before it can accelerate does not deserve the same multiple as one that can deploy capital directly into growth.
Second, debt raises perceived execution risk. If outages, regressions, and security gaps are likely, investors assume revenue targets are less reliable.
Third, debt undermines defensibility. Fragile systems make it harder to expand into enterprise, add new products, or integrate acquisitions. That limits the upside case.
If new funding will pay down code liabilities instead of expanding the business, investors will lower price, add conditions, or walk away.
Valuation drops when your codebase looks like a liability
You do not need a flashy statistic to make this case. Technical due diligence already works this way in practice. Firms that review software for investors routinely assess architecture quality, delivery predictability, security posture, and team dependency because those factors affect scale and investment risk. ThoughtWorks on technical due diligence outlines this clearly.
Founders should treat the codebase as part of enterprise value. A clean system supports faster iteration, better gross margins, stronger retention, and a more believable growth plan. A debt-heavy system does the opposite. It signals that future cash will be spent servicing old decisions.
That is the true cost of technical debt. It does not just make software harder to change. It makes the business harder to trust.
How to Measure and Quantify Technical Debt
A founder walking into a board meeting with "engineering says the codebase is messy" has no case. That language does not justify headcount, explain slower growth, or defend valuation. Measure technical debt the same way you would measure financial debt. Track the balance, track the interest, and identify which liabilities threaten future cash flow.
One useful operating signal is cycle time. Analysts at VFunction on measuring technical debt note that high technical debt can extend the time from commit to deployment by 20% to 50% compared to lower-debt environments. That matters because slower delivery means slower experimentation, slower customer response, and weaker evidence that the business can scale efficiently.
Start with the metrics that matter
Use a short scorecard. You are trying to answer one business question. Is the codebase getting more expensive to change?
Track these signals:
Technical debt ratio: A top-level estimate of remediation cost relative to build cost. It helps you see whether old shortcuts are becoming a material liability.
Cycle time: If shipping gets slower over time, the team is paying interest on past decisions.
Code churn: Files that change repeatedly often point to unstable design, unclear ownership, or unresolved product logic.
Cyclomatic complexity: Complex modules carry more change risk, more test burden, and more room for defects.
These metrics are enough to spot patterns.
A founder should not calculate them manually. Tools such as SonarQube surface complexity, duplication, and code smells inside the development workflow, where they can be reviewed before they turn into due diligence problems.
Add qualitative signals from the team
Numbers show where to look. Engineers tell you why the debt exists.
Ask direct questions in your engineering review:
Which modules does the team avoid touching?
Where do estimates fail most often?
Which areas produce the most rollbacks or hotfixes?
Where does shipping a small change still feel risky?
Patterns matter more than single complaints. If the same systems keep showing up, those systems are carrying hidden liabilities.
Ask the team where they are afraid to make changes. Start there. Fear in the codebase usually maps to future cost.
Use measurement to rank liabilities
Debt metrics are for capital allocation. They are not a founder's weapon for policing engineers.
Treat the codebase like a balance sheet. Some areas support growth. Some areas consume time without producing strategic value. Some areas are one outage, audit finding, or missed enterprise requirement away from hurting a financing process.
A strong technical lead combines tool output, sprint history, defect patterns, and team feedback to rank debt by business impact. That gives you a clear view of what is slowing revenue work, what is increasing operating risk, and what could fail investor technical diligence. That is the standard. If you cannot quantify where engineering capacity is being lost, you cannot defend the startup's growth efficiency or its valuation.
A Founder's Framework for Managing Debt
Not all technical debt is bad. That’s the part most engineering articles get wrong.
A startup should take on debt when the upside is clear, the scope is controlled, and repayment is planned. A startup should reject debt when it touches the foundations of the business or when nobody can explain how and when it gets cleaned up.
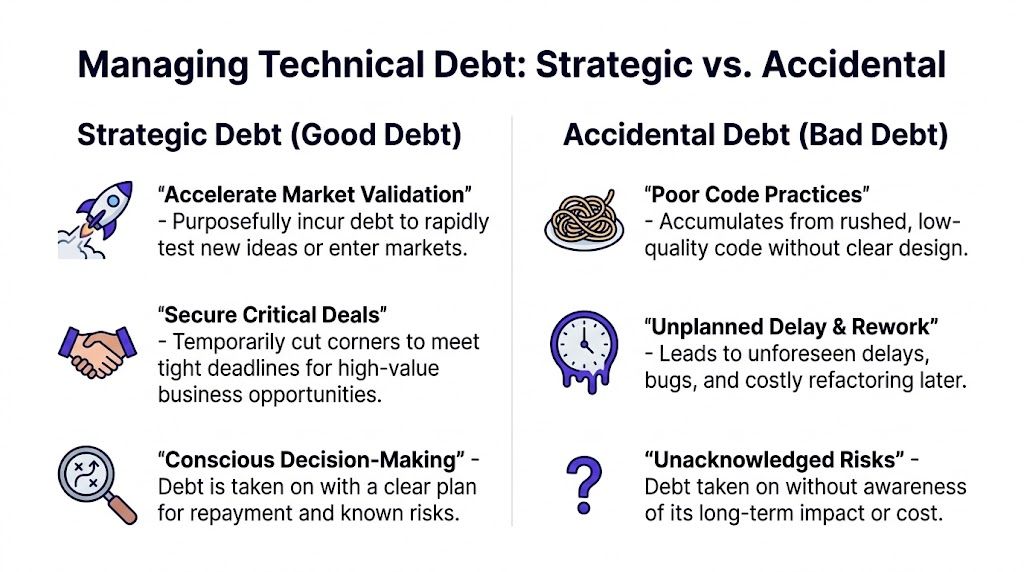
Ask four questions before you borrow against the codebase
When a founder or product lead pushes for a shortcut, I use a simple filter.
Is this in the core of the business
Debt in authentication, payments, permissions, data integrity, and deployment systems is rarely worth it. Those areas become load-bearing quickly. Debt there doesn’t stay isolated.
Is the opportunity time-sensitive
A shortcut is more defensible when it helps validate demand, close a major customer, or test a market assumption that may not persist. If the opportunity isn’t urgent, there’s less reason to borrow against future speed.
Do we have a repayment window
If the team can’t point to the next sprint or two and show where cleanup will happen, the debt is probably not strategic. It’s just deferred pain.
Will this create a precedent
Founders underestimate this one. A one-off exception often becomes the template for future work. If a rushed pattern is easy to copy, your team may repeat it until the whole system bends around the shortcut.
Use a decision table, not gut feel
Question | Strategic debt | Dangerous debt |
|---|---|---|
Why are we doing this | Clear business event or test | Vague pressure to go faster |
Where does it sit | Edge case or temporary path | Core architecture or critical flows |
Who owns repayment | Named owner and backlog item | Nobody |
What happens if it stays | Limited damage | Expanding cost and risk |
The founder’s job is governance
You don’t need to write the refactor plan. You do need to demand decision quality.
That means pushing your team to document shortcuts, define boundaries, and assign owners. It also means resisting the temptation to celebrate every fast delivery equally. Fast work that damages future execution is not efficient. It’s just delayed cost.
Good founders don’t ask engineering to avoid all debt. They ask the team to borrow deliberately and repay predictably.
The companies that scale well aren’t debt-free. They’re disciplined. They know which compromises help the business and which ones subtly erode the product’s long-term value.
Proven Patterns for Debt Mitigation and Repayment
A founder usually feels technical debt when a simple product change turns into a two-week engineering detour right before a customer demo or diligence request. That is debt service. Your team is paying interest in slower releases, higher defect risk, and lower confidence from buyers and investors.
Treat repayment like capital allocation. If debt is hurting speed, reliability, or auditability, put named capacity against it every sprint. IBM recommends reserving part of engineering capacity for debt reduction and maintaining strong test coverage to keep systems maintainable and easier to change, as outlined in IBM’s guidance on technical debt. Track complexity, code churn, flaky tests, and deployment failures, but avoid fake precision. What matters is whether the codebase is getting cheaper to change.
The operating patterns that actually work
Prevention has the highest return.
Raise the bar in code review: Reject duplication, hidden coupling, vague naming, and shortcuts in core flows. If a pattern will spread, stop it before merge.
Run static analysis in CI/CD: Make quality checks automatic and visible on every pull request. Problems found after release already cost more.
Assign code ownership by module: Someone must own maintainability, not just feature delivery. Shared ownership with no accountability creates orphaned debt.
Harden releases: Stable tests, repeatable deployments, and rollback paths turn operational chaos into a controlled process.
If you want an additional tactical perspective, this guide on how to reduce technical debt is a useful companion read.
Repay debt in slices tied to business value
Do not approve broad “cleanup” projects. Approve debt work the same way you would approve any investment. Define the bottleneck, the risk, and the expected payoff.
Use patterns like these:
Refactor high-change modules first. The parts of the system touched every sprint create the biggest tax on delivery.
Add tests before touching fragile code. Repayment without a safety net raises operational risk.
Automate manual release steps. Process debt slows growth just as fast as poor code structure.
Break architecture improvements into shippable stages. Controlled migrations protect revenue and reduce rewrite risk.
This is how you convert engineering effort into valuation protection. Buyers and investors do not reward abstract code quality. They reward a product that can absorb growth without a rescue rewrite.
Match repayment to your development model
Debt reflects team structure as much as code quality. An outsourced team, a small in-house squad, and a founder supported by a fractional CTO need different controls, reporting, and approval paths. This guide to application development models for startups is useful if you need to align ownership and debt policy with the way your product is being built.
What to stop doing
Some patterns destroy value fast:
Stop proposing rewrites because the code feels messy. Rewrite only when targeted fixes cannot remove the business risk.
Stop hiding debt work inside feature estimates. Put it on the roadmap and connect it to release speed, uptime, customer commitments, or fundraising readiness.
Stop spreading effort evenly across the codebase. Concentrate repayment where change frequency, revenue impact, and operational risk intersect.
Your codebase is a balance sheet item. Manage it that way. The goal is a software asset that supports scale, survives diligence, and increases confidence in the company’s future cash flow.
Your Checklist for an Investor-Ready Codebase
Investors don’t fund software that merely works today. They fund systems they believe can survive growth, support enterprise expectations, and absorb roadmap pressure without collapsing into a rewrite.
That means your codebase has to look like an asset under inspection. If you’re building toward a raise, you should already be pressure-testing the product the way a technical diligence team will.
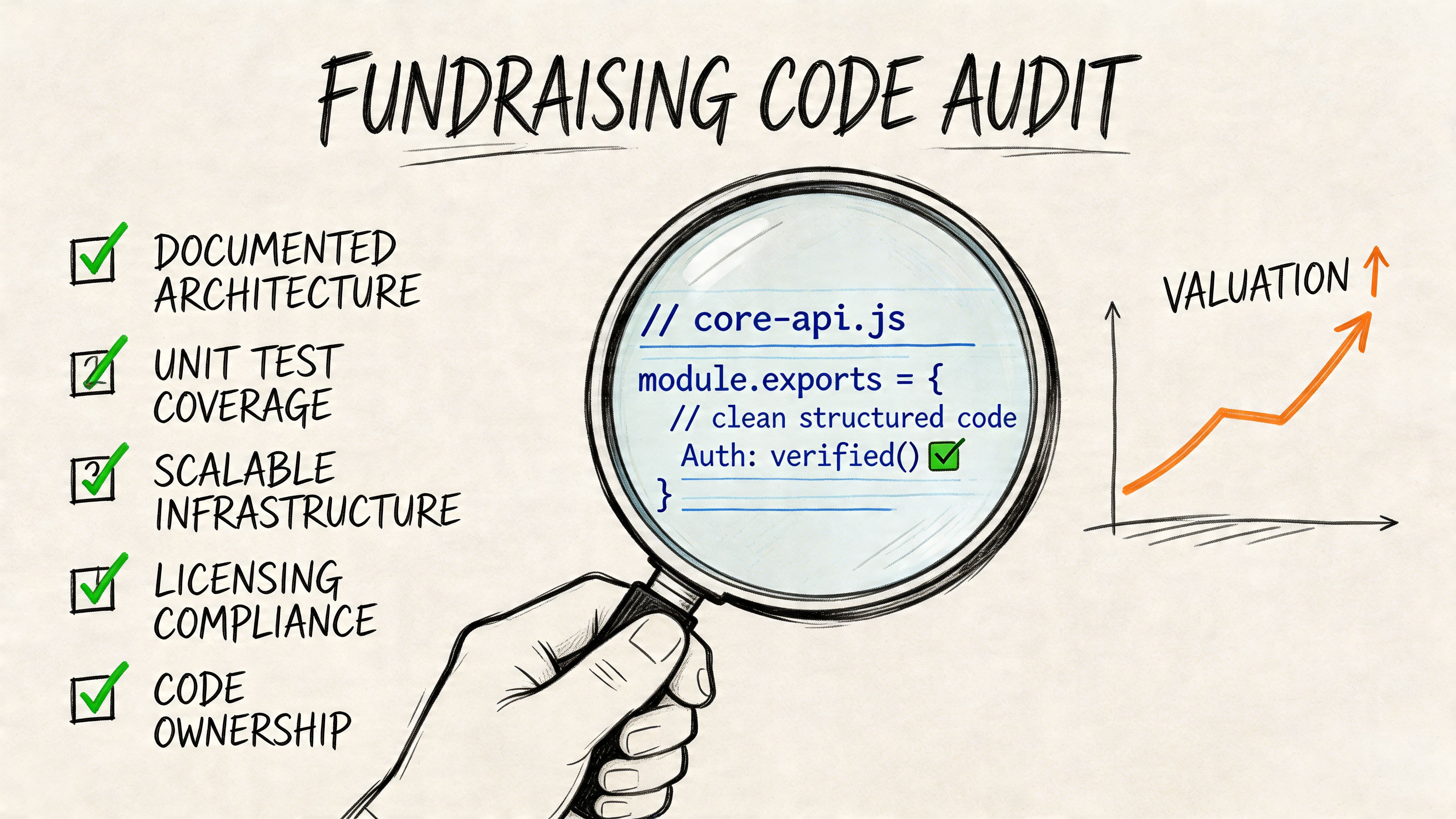
A strong benchmark comes from startup financing itself. A 2025 McKinsey report on over 200 startups found that codebases with a technical debt ratio greater than 15% correlated with 28% lower Series A valuations, because investors flagged them as high-risk during due diligence, as summarized in this Atlassian overview of technical debt and startup risk.
Green flags investors want to see
Use this as a working diligence checklist.
Documented architecture: Your team can explain how the system is structured, why key decisions were made, and where the scaling limits are.
Stable CI/CD pipeline: Builds, tests, and deployments run through a repeatable process instead of tribal knowledge.
Healthy test discipline: Critical paths are covered well enough that changes don’t feel like roulette.
Dependency management: Libraries, frameworks, and infrastructure components are current and reviewed, not drifting unattended.
Visible debt management: The team tracks debt, prioritizes it, and can explain active remediation decisions.
Credible technical leadership: Someone can answer hard diligence questions about trade-offs, system risks, and future scalability.
Red flags that get punished
In this context, valuations soften fast.
Red flag | What investors infer |
|---|---|
No clear architecture narrative | The team has built reactively |
Manual deployments | Reliability depends on people, not systems |
Critical flows with weak tests | Future growth will increase release risk |
Large unexplained legacy areas | The company may need major remediation after funding |
Untracked technical debt | Leadership doesn’t understand technical risk |
A founder-ready audit pass
Before fundraising, sit down with your CTO, fractional CTO, or engineering lead and demand direct answers.
Ask for:
A list of risky modules and why they’re risky
The current debt management plan
Evidence that deployment and testing are repeatable
A roadmap showing how the system supports growth
A clear explanation of any debt intentionally carried forward
If you’re preparing an MVP for scrutiny, this guide to an investor-ready MVP is a practical next read because product validation and technical diligence need to line up.
The founder takeaway is simple. Your codebase is part of your valuation story. Clean, well-governed systems tell investors your company can scale. Chaotic systems tell them their capital will disappear into repair work.
If you want a technical partner who treats your product like an investable asset, not a disposable prototype, talk to Buttercloud. We help founders turn ideas into production-grade MVPs, strengthen technical architecture before due diligence, and build codebases that support growth, reliability, and stronger valuations.